Three layers of cryptographic protection, and why the platform that holds your keys is the wrong platform.
 By Admin
By AdminThe Bitcoin Address That Cannot Be Drained — Even If My Server Gets Hacked
In 2014, Mt. Gox lost 850,000 bitcoin. In 2019, Binance lost 7,000. In 2022, FTX lost — well, you know. Every time a Bitcoin exchange or escrow service collapses, the same headline runs: "Customer funds drained." And every time, retail users learn the same lesson the hard way: when somebody else holds your keys, your coins are not really yours.
So here is a deliberately provocative claim, and then I will show you the math. There is a way to design a Bitcoin address that cannot be drained — even if the platform that created it is completely compromised. Even if every server is on fire. Even if the company filed for bankruptcy yesterday.
This is not theoretical. We built it. It is called TapVault, it is free, and the architecture relies on three layers of cryptographic protection — each one independently sufficient to defeat the attack. Here is how it works.
The setup — what we are protecting
Imagine you are a buyer. You want to purchase a domain name from a stranger for $5,000 in Bitcoin. You do not trust them, and they do not trust you. You both decide to use an escrow platform.
Normally, here is what happens. You send Bitcoin to the platform's wallet. They hold it. When the seller transfers the domain, you tell the platform to release the funds. The platform sends the BTC to the seller. Done.
Now imagine the platform's hot wallet keys leak overnight. Your Bitcoin — and everyone else's — vanishes. There is nothing the platform can do, because the attacker now has the same control they did. This has happened. Repeatedly. It is the default mode of failure for custodial Bitcoin services.
TapVault is designed so that this exact attack does not work. Here is the diagram, then the explanation:
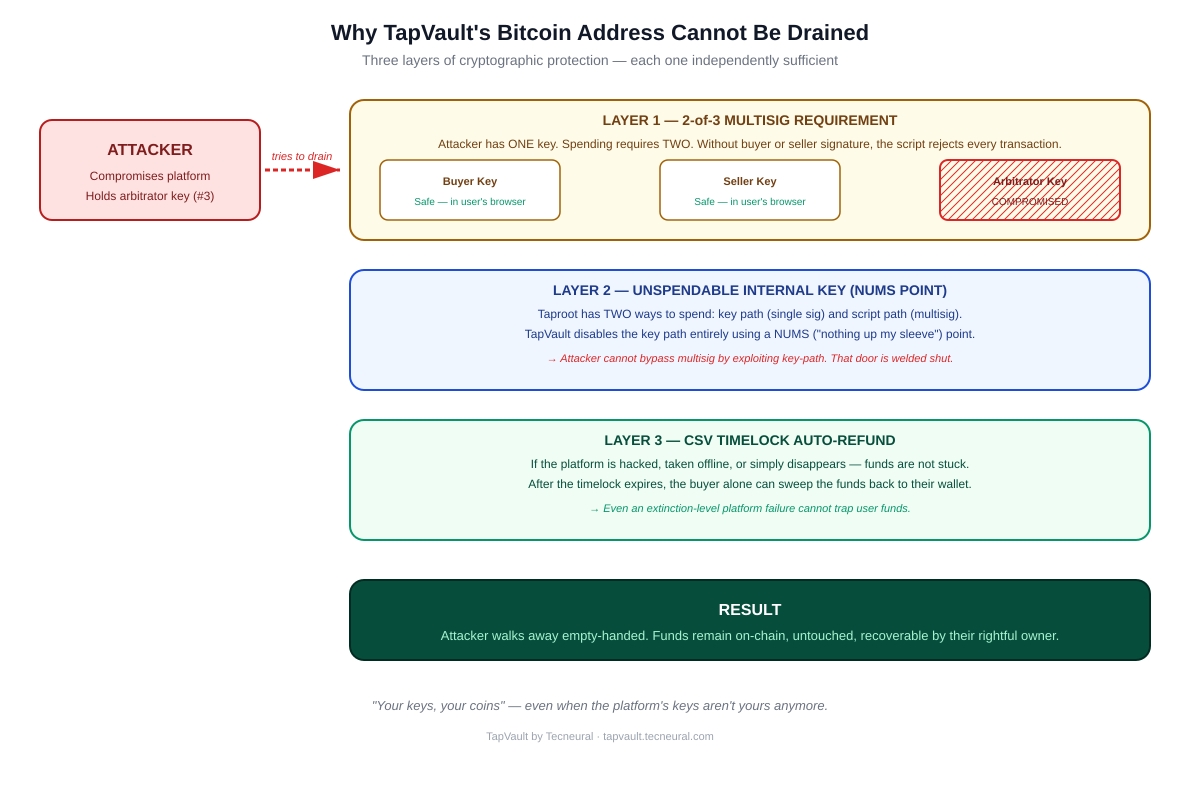
Layer 1 — The 2-of-3 multisig requirement
When you create an escrow on TapVault, the platform does not deposit your funds into a wallet it controls. Instead, it derives a brand-new Taproot address that is locked by three keys — yours, the seller's, and the platform's (the arbitrator key). To move funds, two of those three keys must sign.
So if an attacker compromises the platform and steals the arbitrator key, they have one signature. The Bitcoin script requires two. Without your key or the seller's key — both of which live in your respective browsers, encrypted with passwords only you know — the attacker cannot produce a valid transaction. The blockchain rejects every attempt.
This is not a permission system. It is not a policy. It is enforced by Bitcoin itself — by the global network of nodes that validate every transaction. The platform cannot override it any more than it can override gravity.
Layer 2 — The unspendable internal key
Here is where Taproot does something clever. Taproot addresses have two ways to spend. The "key path" lets a single signature spend the output (cheaper, more private). The "script path" requires fulfilling a complex script — like our 2-of-3 multisig.
If we naively used Taproot, the platform might be tempted to embed a backdoor key path that lets it spend funds unilaterally. Even if it never used that backdoor, the existence of the backdoor would make the entire system custodial in disguise.
TapVault eliminates this risk. The internal key — the one that would normally control the key path — is set to a NUMS point. NUMS stands for "Nothing Up My Sleeve." It is a Bitcoin point that is provably not associated with any private key. Anyone can verify, with simple math, that no signature exists for it. The key path is not just unused — it is mathematically unspendable.
Result: the only way to move funds out of the address is the script path, which is the multisig requirement from Layer 1. There is no backdoor because there is no door at all.
Layer 3 — The CSV timelock auto-refund
So we have established that the platform cannot drain funds with one key, and there is no key-path backdoor. But there is one more failure mode to consider — what if the platform simply disappears?
Maybe the company gets sued out of existence. Maybe the team quits. Maybe the servers get seized by a regulator. In a normal multisig setup, this would be catastrophic — funds would be locked forever, requiring two signatures with one signer permanently unavailable.
TapVault solves this with a CSV timelock. Embedded in the script tree is a fourth spend path: after a configurable number of blocks (typically a few weeks), the buyer alone can sweep the funds back to their own wallet. No platform involvement. No arbitrator. Just the buyer, signing with their own key, claiming back what is theirs.
In the worst-case scenario where everything goes wrong — platform hacked, team gone, servers offline — the timelock guarantees that funds eventually return to the rightful owner. Bitcoin honors the script forever, regardless of what happens to TapVault.
The full attack matrix
Here is how the system holds up against every realistic attack a custodial platform faces:
| Attack scenario | Custodial outcome | TapVault outcome |
|---|---|---|
| Hot wallet keys leaked | All funds drained instantly | Attacker has 1 of 3 keys — no funds move |
| Database breached | PII + balances exposed | PII at risk; funds remain on-chain |
| Insider goes rogue | Internal admin can move funds | No admin can move funds alone |
| Platform shuts down | Funds locked or lost | Timelock auto-refunds buyer |
| Court orders seizure | Platform must comply | Platform has nothing to seize |
"But surely there is some way?"
Skeptical readers — and I encourage you to be — usually push back with one of three questions. Let me address them directly.
"Could a sophisticated attacker forge signatures?"
Only by breaking Schnorr signatures themselves — which would also break the entire Bitcoin network and roughly $1 trillion of value. If that happens, escrow is the least of anyone's problems.
"Could the platform secretly use a different address than the one shown to users?"
Each user's browser independently derives the expected address from the three public keys and verifies it before depositing. If TapVault tried to substitute a different address, the verification would fail and the deposit would never happen. This check is open-source and runs locally.
"What about quantum computers?"
A real concern — but a concern for all of Bitcoin, not just escrow. When the network migrates to post-quantum signatures, TapVault migrates with it. The architecture is signature-scheme-agnostic; only the cryptographic primitive changes.
Why this matters beyond escrow
Non-custodial design is not just a security improvement — it is a regulatory one. A platform that holds customer funds is, in many jurisdictions, a money services business. That triggers KYC requirements, capital requirements, audit obligations, and a long tail of compliance overhead.
A platform that never holds customer funds — that exists purely as a coordinator and arbitrator — operates in a fundamentally different regulatory category. The exact treatment varies by country, but the principle is the same: you cannot regulate the custody of funds that the platform never custodied.
This is why we believe non-custodial architecture is the future of Bitcoin commerce. Not because users demand it — most users do not even know to ask. But because operators eventually realize that holding other people's money is the worst job in fintech.
How to verify any of this for yourself
You do not have to take our word for it. Every one of the claims above can be verified independently.
- Read the TapVault source code — the address derivation logic is in a single file
- Generate a test escrow on testnet, observe the bc1p... address, and verify the script tree using a Taproot inspector tool
- Try to spend the funds with only the arbitrator key — Bitcoin will reject the transaction
- Wait for the timelock to expire and sweep with only the buyer key — it works
This is the entire point of trustless infrastructure. You do not need to trust the team that built it. The math is the trust.
Closing thought
The Bitcoin community has been saying "not your keys, not your coins" for over a decade. It is usually invoked to discourage people from leaving funds on exchanges. But it applies to escrow with equal force.
If your escrow platform can drain your funds, it is not really escrow. It is just a custody product with extra steps.
Tecneural built TapVault because we believe the cryptographic primitives that make true non-custodial escrow possible — Taproot, MAST, Schnorr, NUMS, CSV timelocks — are too important to be locked behind paywalls or closed-source codebases. Take it. Run it. Verify everything. That is the whole point.
GET TAPVAULT — IT'S FREE
TapVault is open and free. Reach out to Tecneural and we will send you the source code, deployment guide, and a 30-minute setup call.
Live demo: tapvault.tecneural.com
Get the code: Contact Tecneural — we ship the repository to qualified teams
Larger projects: Bitcoin L2, BitVM bridges, custom AI models — also Tecneural
About the author
Jeyakumar S — CEO at Tecneural. 16+ years building Bitcoin Layer-2 infrastructure, threshold signature systems (FROST, Schnorr aggregation), validator coordination, and cross-chain bridge primitives. Specializes in Rust and C++ cryptographic systems and consensus-layer engineering.
Contact Us
- 📞 Phone: +91 96555 17034
- 📧 Email: support@tecneural.com
- 🌐 Website: www.tecneural.com
 Predictive Analytics & Forecasting Systems
Predictive Analytics & Forecasting Systems Intelligent Process Automation (AI + RPA)
Intelligent Process Automation (AI + RPA) Custom LLM / Domain-Specific Model Development
Custom LLM / Domain-Specific Model Development Generative AI Solutions (Text, Image, Code, Voice)
Generative AI Solutions (Text, Image, Code, Voice) AI Chatbots, Virtual Agents & AI Co-Pilots
AI Chatbots, Virtual Agents & AI Co-Pilots Enterprise Knowledge Bots (Docs, CRM, ERP AI)
Enterprise Knowledge Bots (Docs, CRM, ERP AI) Natural Language Processing (NLP) Solutions
Natural Language Processing (NLP) Solutions Computer Vision & Video / Image Analytics
Computer Vision & Video / Image Analytics Recommendation Engines & Personalization Systems
Recommendation Engines & Personalization Systems Fraud Detection & Anomaly Detection Models
Fraud Detection & Anomaly Detection Models AI-Powered Decision Support Systems
AI-Powered Decision Support Systems AI-Driven Marketing & Campaign Automation
AI-Driven Marketing & Campaign Automation MLOps, Model Deployment & Monitoring
MLOps, Model Deployment & Monitoring AI Governance, Risk & Compliance Advisory
AI Governance, Risk & Compliance Advisory AI Strategy, Roadmaps & Use-Case Discovery
AI Strategy, Roadmaps & Use-Case Discovery